A study on occupational fraud published by the Association of Certified Fraud Examiners (ACFE) found that organizations around the world are losing an estimated five percent of their annual revenues to internal theft.
Any organization, irrespective of its size, can be exposed to employee fraud. The nature of such frauds can be financial, asset misappropriation, data theft, and identity theft, amongst others.
However, when it is a single fraudster trying to make a quick buck versus a fraud ring, the need to detect and prevent them becomes even more important.
In fact, the attacks that are made by fraud rings are more technical and methodical in nature.
But what is actually a fraud ring?
A fraud ring is a group of people who form a coalition to undertake activities with the aim of taking advantage of others, cheating them, or defrauding them.
In this article, we will discuss the five top rules that will aid the Human Resource (HR) department in detecting and preventing fraud rings.
5 Important Rules for HR to prevent and detect fraud rings online
The downside of any fraud is that it results in a financial loss to the company, as well as a loss of its reputation and its customers or clients.
The trouble with identifying fraud rings is that the organization always views them through its own lens. What is needed is a multi-layered approach to tackle the problem from all angles.
An organization should:
- Think along lines of a fraudster as that will help them come up with creative approaches to fraud prevention
- Facilitate as much internal collaboration as possible, though at times it becomes difficult due to the organizational structure
- Network within and outside their industries and learn more about what frauds others are seeing
Some of the most common examples of fraud rings are credit card fraud rings, identity theft fraud rings, money laundering fraud rings, and so on.
The most obvious question is how do we prevent them, but more importantly how do we detect them.
1. Start with background check data
To use a cliché, prevention is always better than cure.
As an HR professional, you must always ensure you hire a trustworthy employee for your organization.
An extensive background check of the potential hire is an effective way to determine this. This check can reveal many facts about the employee, which may raise red flags.
Never overlook conducting background checks on potential or new recruits, even though they may seem unnecessary or neurotic.
Background checks consisting of criminal and credit checks will help to identify the past criminal history of the hire.
- They will easily identify any future financial obligations, like a loan repayment or card bill that is due.
- They may reveal enhanced wages that may indicate prior embezzlement.
It is always better to start with as much data as possible. As much more you start with, it will be better to spot connections later.
2. Conduct regular internal audits

The incidences of fraud related to finance are on the increase.
In a banking setup, if there are frequent or strange changes to a customer account, these are positive indicators of different types of banking frauds.
It is estimated that in 2019 financial fraud was 6% of the Gross Domestic Product (GDP), or over $5 trillion.
Fraudsters are always on the lookout for a gap in your organization’s fraud detection solution.
Once they discover it, they will deploy several tactics and strategies to penetrate the organization’s database to get what they need to perform the fraud.
As an organization, you need to be proactive to meet the threats posed by fraud rings and keep your fraud protection system up to date.
The system should:
- Ensure that the organization’s payment solution can analyze customer data
- Prompt detection of new or unknown IP addresses in the database
- Have the ability to avoid being detected and overturned by the fraudsters
Regular audits are a regular part of a good organization. To prevent online fraud, it is necessary to perform a security audit. This will enable cyber security experts to determine where the weak points in the organization’s systems exist.
Patching these weak points can make it less likely for fraud rings to carry out online fraud.
When fraud has occurred, the internal audit should be able to pinpoint how the controls failed and identify opportunities for improvement.
Also, organizations need to understand that fighting online fraud is a team effort. A top-down approach is needed where the company leaders prioritize online fraud fighting and encourage the employees to follow suit.
All employees should be trained to know what might constitute fraud rings and what will be their action steps when they detect any such activity.
3. Utilize data collection and enrichment
Understandably, data is the key to gathering information about the possibility of a fraud ring. Fraud rings can be easily detected by gathering user data, like their email addresses or phone numbers.
In most cases, you can extract the data from the given sources, and other times, you need to go and look for it.
This process is called data enrichment.
Data enrichment adds to the information you have about your users without having to ask them to provide additional information.
A few examples of enriched data would like this:
- The social media profiles are linked to the phone numbers or email addresses of the users.
- If their card numbers indicate that it is a prepaid card.
- Whether their IP address points to an authorized VPN or a proxy.
Overall, it is a great way to know more about your users’ journeys without causing any kind of conflict.
4. Use data analytics to look for patterns and links
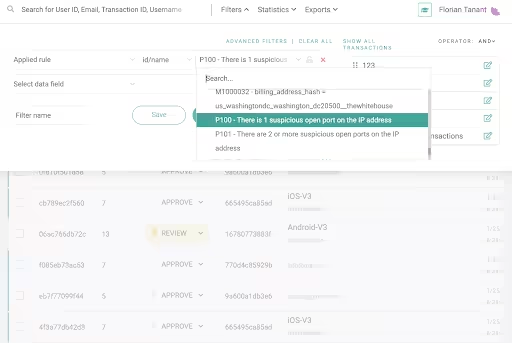
Once you have the maximum amount of data possible, now look for patterns.
The key to detecting fraud rings is the timely discovery of anomalous patterns in the data. This is a red flag that signals unusual activity is occurring which must be halted immediately to prevent fraud.
From the above image, it is clear that we are looking at transactions that originated from a suspicious IP.
In any case, we can choose to be selective with our data findings by including a date range or by using a stronger filter that looks at device data.
Fraud rings usually have access to a lot of data and they typically use device spoofing methods to access the most powerful data. These could either include device operating systems or the plugins that have been installed and even the attempts made by them to hide behind both software and hardware emulators.
Once this is done, you need to visualize the connections with graphs to establish the link between users.
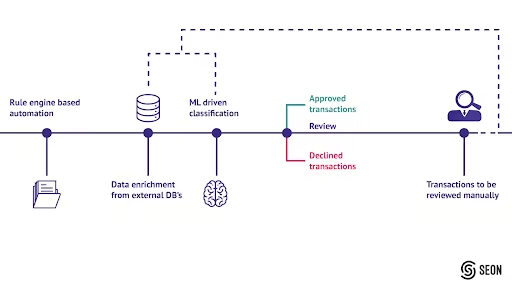
Use machine learning
After data analytics, the next level is Machine Learning (ML). In ML, algorithms are studied and applied to extract data and enable inferences based on statistics.
These algorithms run through the data you have collected and suggest possible patterns. Machine learning develops data from the information provided, which will aid the organization in making decisions, as well as predictions.
5. Have a whistle-blower hotline in place
Reporting any wrong activity or fraud suspicions may intimidate even the most loyal employee.
Having a system in place for employees, customers, and even suppliers to report such issues anonymously is quite important.
Whistle-blowing procedures and policies are important tools in any organization to improve the responsible behavior of employees.
A fraud hotline can aid an organization in preventing fraudulent behavior. It can also detect issues before they become serious, reduce losses that could hurt the company, and promote a healthy work environment.
It is vital that they are anonymous. Employers can receive important anonymous tips from their employees. On the other hand, employees can report wrongful behavior anonymously, without being afraid of any retaliation.
An anonymous reporting system of wrongdoing will make employees more confident to report such activities, as they know their names won’t be attached to their tips. They will not have to fear retaliation.
By reporting the issue through the hotline, the employees could end up saving the organization money and even lives, thanks to early detection and correction.
The US Federal Law, the Sarbanes-Oxley Act of 2002, requires publicly traded companies to provide a confidential method for employees to report fraudulent activities or wrong behavior in the organization.
The American Institute of Certified Public Accountants (AICPA) has recommended that all organizations, publicly traded or not, implement a whistle-blower system for reporting wrongdoing or illegal activities.
With an anonymous whistle-blower hotline in place for employees, tips can be submitted safely and securely for all manner of wrongdoing.
Conclusion
If you are an HR manager, the tips mentioned above will definitely help in reducing the risk of online fraud rings in your organization.
Any organization is prone to online fraud attempts. It is the awareness that helps businesses to fix the potential fraud and know best how to address the challenge.
The suggestions here will help your organization get on to a strong start in effectively curbing the problem and noticing which tactics are most appropriate for it.
Let us know in the Comments section below if you follow any other rules to prevent and detect online fraud rings in your organization.
.avif)
